To make Nagios CORE security compliant with a SHA2/SHA256 cert, follow these steps using Openssl and you will be ready in no time with a PCI compliant cert. This is a standard requirement nowadays in any PCI compliant environment. This is...
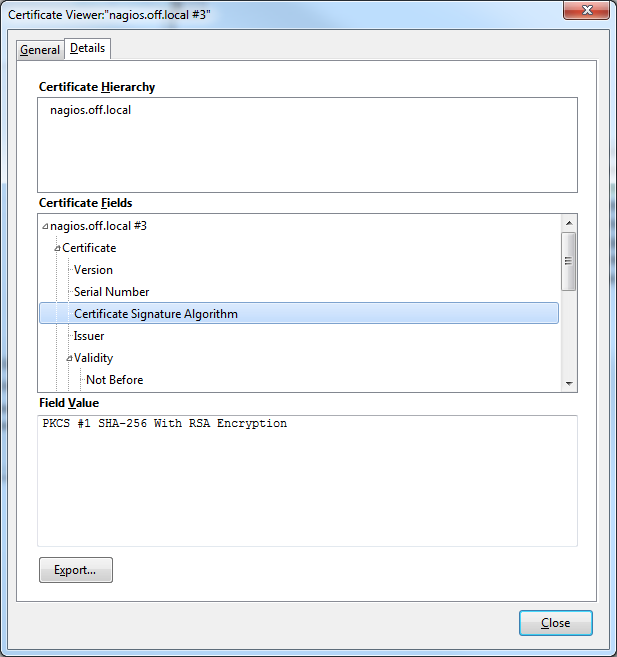
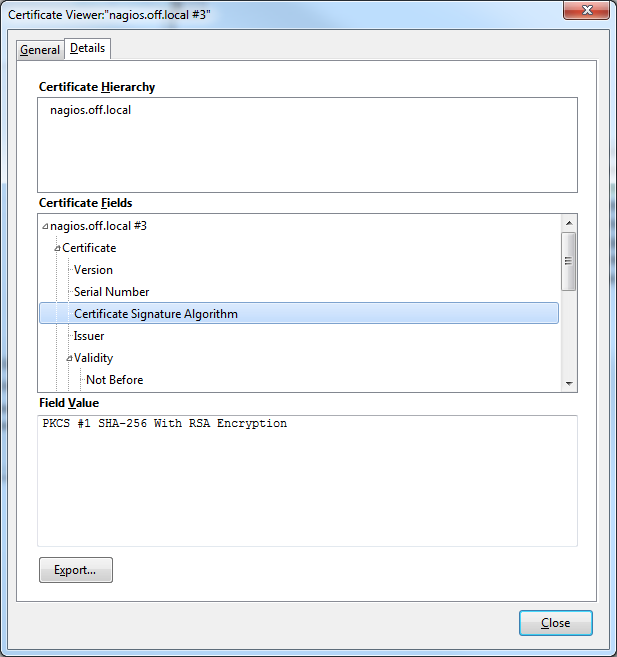
To make Nagios CORE security compliant with a SHA2/SHA256 cert, follow these steps using Openssl and you will be ready in no time with a PCI compliant cert. This is a standard requirement nowadays in any PCI compliant environment. This is...

This script is to monitor a failure when Nagios daemons fails to start or sometimes Nagios stops sending alerts. When you check the logs at "/usr/local/nagios/var/log/nagios.log" you might come across messages like "Caught SIGSEGV,...

Its possible to upgrade Nagios CORE to the latest version by just following these simple steps. This article covers upgrade, backup and restore in case of a failure.The Latest Version of Nagios CORE is 4.2.4 as of January,2017 for which...

Its possible to enable SSL over http for Nagiso Core (Red Hat/CentOS). The Nagios WEB UI can be made secure by enabling https instead of plain http in Nagios. After you are done installing Nagios Core in Linux, you need to enable OpenSSL...